Specialist Cybersecurity Services [ contact: Special Projects ]
These interim services (subject to HMRC IR35 pre-assessment) involve taking IT security to a higher level as required within legal or regulatory compliance policy, (often as a response to serious or high impact incident) that defines a more cogent and compelling security stance against highly capable, motivated, well-resourced and determined attackers. The services may involve the preparation of some combination of a series of advanced facilities and include Reserqarch and Development (compliant with the definition proffered by HMRC).
CDD's bespoke services are geared to organisations that have access to a higher degree of knowledge of their own environment, appropriate skills and capabilities, and are responding to a threat presence that demands engineering commensurate with a level of risk arising from highly proficient cyberattackers targeting high value, mission critical IT assets which may imply serious organisational consequences if they achieve successful compromise.
A new approach to AI security assurance is available from CDD. The ZICONIA® methodology provides an advance on conventional CIA which has shown to be inadequate for contenporary cyber security involving artificial intelligence based processes.
CDD is also able to offer a temporary consultancy service encompassing the role of Interim Chief Information Security Officer (ICISO) or senior interim board level Chief Technology Officer (CTO) for organissations that require fresh minds on their IT security problem space.
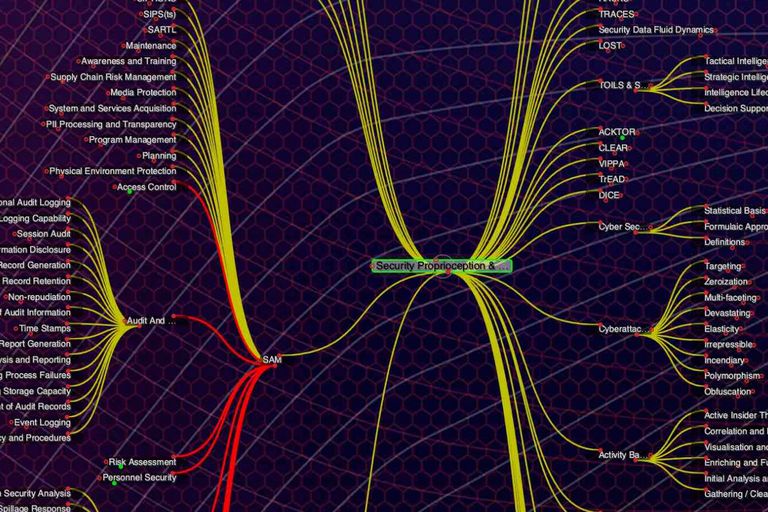
Prepare Formal Threat Targeting and Cyber Response:
● Activity Based Intelligence
● Advanced Threat Profiling
● Threat Hunting & Forensics
In response to high-impact cyberattack upon mission critical assets, it is necessary to consider and understand how such highly capable attackers behave.
CDD can prepare best mechanisms (involving tools and processes that may already be available in their IT arena) for organisations to achieve such understanding, which will be essential for mitigation of risk arising from such individuals or groups.
Identify Orchestrated Cyber
Security Combinetrics:
● Combined Vulnerabilities
● Combined Vectors
● Consequential Impact
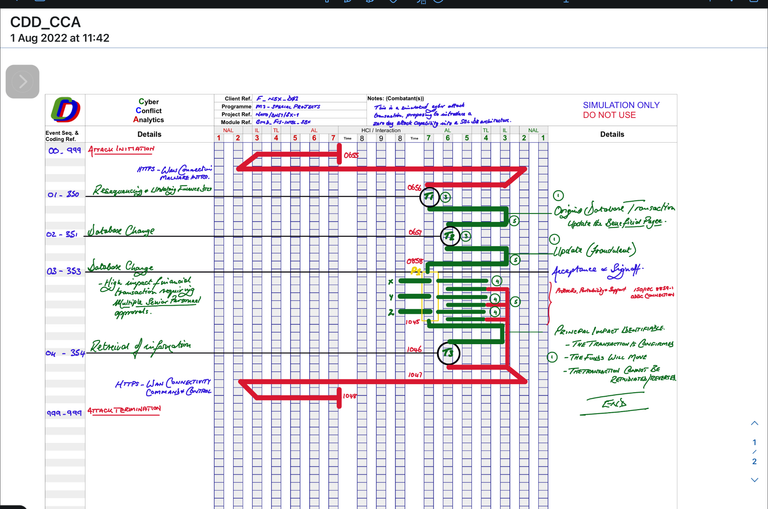
High-impact cyberattack frequently involves the combination of a number of simple but carefully orchestrated facets that constitute complicated attack behaviour. Unless the requisite depth of cybersecurity situational awareness is achieved, and the precise nature of vulnerabilities properly understood, such attacks may go unnoticed (and for extended periods of time), and with very great impact and consequences. This is referred to as OPTIMIZED attack.
CDD can apply its systems to discern the many routes of combinatorial cyberattack and propose appropriate mitigation and response.

Undertake Advanced
Service/Crypto Integration:
● Tool/Protocol Analytics
● Advanced Cyber Awareness
● Cyber Risk Transmutation
Many organisations are well equipped in terms of both toolsets and skillsets. However, too much data or 'information overflow' can be a serious impediment to effective response and rapid resolution of serious cyberattack. It is critical to rapidly understand the precise nature of such attack, but without cluttering complex decision making processes that are critical to effecting success response.
CDD is able to advise on methods to integrate processes and toolsets to better utilise security enforcing functionality and provide decision makers and technicians with only the necessary information they can properly use. This is an essential first step in turning the risk of cyberattack back on the threat-actors.